Blogs
Each of us has his own preferences: some people love Lady Gaga or Justin Bieber, others Rocco Siffredi or Laura Lion. The love for the latter can be dangerous if you are not aware of security problems when you have a non-updated system, and it's possible you end with an infected system asking for money to recover the control of the machine.
This was an interesting situation so I tried to help my friend. In this case, just after the desktop appeared, a full-screen window showed. It was a warning from the Spanish police ("Cuerpo Nacional de Policía") saying that the system had been blocked because it had been used to perpetrate illegal actions like child pornography, terrorism and violence against children: " Fue detectado un caso de actividad ilegal. El sistema operativo fue bloqueado por violación de las leyes de España!". A warning like this can be shocking for a normal user, so social engineering was working here. However, this warning was also asking for 100€ to be paid via Ukash or Paysafecard as a fine for this behaviour and in order to restore the system. This part can be a bit strange and maybe makes the victims call the police very quickly. Once this window appeared no other action was possible, like execute the Task Manager or return to the desktop, just enter a code to pay.
Submitted by jesparza on Mon, 2012/02/06 - 20:13
Maybe it was not evident enough or not well documented, but until the moment there was a way of extracting streams, Javascript code, shellcodes and any type of information shown in the console output. What it's true is that it was not very straightforward. To extract something it was needed to set the especial variable "output" to a file or variable in order to store the console output in that new destination. For this to be accomplished we used the set command and after this the reset command to restore the original value of "output".
PPDF> set output file myFile
PPDF> rawstream 2
78 da dd 53 cb 6e c2 30 10 bc f7 2b 22 df c9 36 |x..S.n.0...+"..6|
39 54 15 72 c2 ad 3f 40 39 57 c6 5e 07 43 fc 50 |9T.r..?@9W.^.C.P|
6c 1e fd fb 6e 4a 02 04 54 a9 67 2c 59 9e 9d f5 |l...nJ..T.g,Y...|
8e 77 56 32 5f 9c 6c 9b 1d b0 8b c6 bb 8a 15 f9 |.wV2_.l.........|
2b cb d0 49 af 8c 6b 2a b6 fa fc 98 bd b3 45 fd |+..I..k*......E.|
92 d1 e2 27 15 e6 b4 33 aa 70 b1 47 15 db a4 14 |...'...3.p.G....|
e6 00 2e e6 42 f9 35 e6 d2 5b a0 04 b0 73 09 15 |....B.5..[...s..|
a1 aa 77 22 08 0e 04 46 4e 7a a7 4d 43 3a 92 84 |..w"...FNz.MC:..|
2e 22 c7 e3 31 b7 46 76 3e 7a 9d 72 df 35 10 e5 |."..1.Fv>z.r.5..|
06 ad 80 93 34 50 e6 6f 57 51 92 08 1d 46 74 e9 |....4P.oWQ...Ft.|
ca f4 9c d2 b7 31 31 83 af ba e0 30 c2 e9 05 bd |.....11....0....|
55 bb 36 8a ad f6 2a fc 1e 61 ab e8 5a ad 39 fc |U.6...*..a..Z.9.|
95 9a 0a 18 97 b0 13 32 99 03 f6 af dc 86 b7 ad |.......2........|
Submitted by jesparza on Tue, 2012/01/24 - 21:49
After the exploit static analysis some things like the function of the shellcode were unclear, so a dynamic analysis could throw some light on it. When we open the exploit without the Javascript code used for heap spraying we obtain an access violation error in rt3d.dll. If we put a breakpoint in the same point when we launch the original exploit we can see this ( better explanation of the vulnerability):
Instead of showing an access violation the CALL function is pointing to a valid address in icucnv36.dll, 0x4A8453C3. This address is not random and it's used in the Javascript code to perform part of the heap spraying:
Submitted by jesparza on Mon, 2012/01/23 - 17:30
CVE-2011-2462 was published more than one month ago. It's a memory corruption vulnerability related to U3D objects in Adobe Reader and it affected all the latest versions from Adobe (<=9.4.6 and <= 10.1.1). It was discovered while it was being actively exploited in the wild, as some analysis say. Adobe released a patch for it 10 days after its publication. I'm going to analyse a PDF file exploiting this vulnerability with peepdf to show some of the new commands and functions in action.
As usual, a first look at the information of the file:
I've highlighted the interesting information of the info command: one error while parsing the document, one object (15) containing Javascript code, one object (4) containing two ways of executing elements (/AcroForm, /OpenAction) and one U3D object (10), suspicious for its known vulnerabilities, apart of the latest one.
So we have several objects to explore, let's start from the /AcroForm element (object 4):
Submitted by jesparza on Mon, 2012/01/16 - 18:22
I've received a Christmas gift some hours ago. In fact there were two gifts but only one has survived the trip. They are from Russia...with love. Of course I'm talking about two e-mails I've received with two suspicious links. Even the e-mail bodies were suspicious, I think they have packed very quickly my gifts or they are not very attentive to me...:( The From field included "bankofamerica" and the Subject "Accountfrozen" so I suppose this means that my Bank of America account is frozen, right?
After some redirections we can find the typical obfuscated Javascript code made in BlackHole:
After decoding the Javascript code we obtain the next step, also related to BlackHole. This time I can only see a unique Flash exploit trying to download and execute a binary from the same domain where the exploit kit is located (shellcode is XORed with 0x28).
Submitted by jesparza on Thu, 2011/12/29 - 03:31
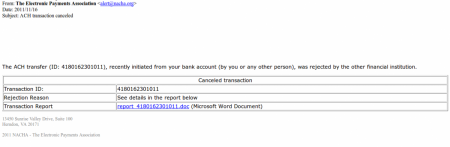
Our team (S21sec) has detected a ZeuS trojan distribution by email campaign that has been running for some days. The malicious emails include a link to a supposed report about a cancelled transaction, which is actually an HTML page that loads Javascript code into the victim’s browser. This code tries to exploit different vulnerabilities in Java, Flash and PDF to install ZeuS 2.0 on the system. This is one of the latest versions of ZeuS which uses P2P as part of its infrastructure (Murofet 2.0).
The subject of the emails detected so far is “ACH transaction canceled” and in the body of the mail there is information about a supposed transaction that has been cancelled. If the victim wants further information then they have to visit a link that contains a report about the transaction:
For a few seconds the victim sees a screen indicating that they must wait. Meanwhile 4 scripts, stored on different domains are loaded into user’s browser. They are little more than simple redirections towards the site where the code (that will attempt to perform the exploitation) resides.
Submitted by jesparza on Tue, 2011/11/29 - 14:02
According to a Kaspersky Lab article, SEO Sploit Pack is one of the Exploit Kits which appeared in the first months of the year, being PDF and Java vulnerabilities the most used in these type of kits. That's the reason why I've chosen to analyse a malicious PDF file downloaded from a SEO Sploit Pack. The PDF file kissasszod.pdf was downloaded from hxxp://marinada3.com/88/eatavayinquisitive.php and it had a low detection rate. So taking a look at the file with peepdf we can see this information: In a quick look we can see that there are Javascript code in object 8 and that the element /AcroForm is probably used to execute something when the document is opened. The next step is to explore these objects and find out what will be executed:
Submitted by jesparza on Mon, 2011/11/14 - 01:03
I'm going to lay aside PDF files and malware to write a simple script to control friends and followers on Twitter. We use to have a lot of them and it's difficult to know if our friends haven't written some time ago or our followers have left. But we can use one of the multiple modules (talking about Python) to communicate with the Twitter API and solve this task. I've chosen Tweepy because I think it's very simple and well documented. What we want to obtain from Twitter is: It's important to highlight that we cannot obtain all the friends/followers with one API request but only 100 each time. We can use the Cursors object from Tweepy to solve this very easily:
followersCursor = tweepy.Cursor(tweepy.api.followers,id=user)
for follower in followersCursor.items():
print follower.name
Submitted by jesparza on Tue, 2011/08/16 - 20:35
After the "useless" analysis of the fake objects now we can focus on the objects which will be parsed by the PDF reader:
/Catalog (27)
dictionary (28)
dictionary (22)
dictionary (23)
dictionary (22)
/Annot (24)
dictionary (23)
/Page (25)
/Pages (26)
/Page (25)
stream (21)
/Pages (26)
If we take a look at the Catalog object...
PPDF> object 27
<< /AcroForm 28 0 R
/MarkInfo << /Marked true >>
/Pages 26 0 R
/Type /Catalog
/Lang en-us
/PageMode /UseAttachments >>
There is no presence of any triggers here (/OpenAction) or in the rest of the objects (/AA) so it seems that the /AcroForm element has something to say. Also, the suspicious object 21 (/EmbeddedFile) is related with this interactive form:
PPDF> references to 21
[28]
PPDF> object 28
<< /DA /Helv 0 Tf 0 g
/Fields [ 22 0 R ]
/XFA [ template 21 0 R ] >>
In the dictionary of the form we can see that object 21 is a template and that there is a reference to a field object (object 22). So we continue analysing the field objects:
PPDF> object 22
<< /V
Submitted by jesparza on Tue, 2011/07/26 - 21:30
In past November The Honeynet Project published a new challenge, this time related to PDF files. Although it's quite old I'm going to analyse it with my tool because I think it has some interesting tricks and peepdf makes the analysis easier. The PDF file can be downloaded from here.
If we launch peepdf we obtain this error:
$ ./peepdf.py -i fcexploit.pdf
Error: parsing indirect object!!
It seems that there is an error in the parsing process. Talking about malicious PDF files it's recommended to add the -f option to ignore this type of errors and continue with the analysis:
$ ./peepdf.py -fi fcexploit.pdf
File: fcexploit.pdf
MD5: 659cf4c6baa87b082227540047538c2a
Size: 25169 bytes
Version: 1.3
Binary: True
Linearized: False
Encrypted: False
Updates: 0
Objects: 18
Streams: 5
Comments: 0
Errors: 2
Version 0:
Catalog: 27
Info: 11
Objects (18): [1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 22, 23, 24, 25, 26, 27, 28]
Errors (1): [11]
Streams (5): [5, 7, 9, 10, 11]
Encoded (4): [5, 7, 9, 10]
Objects with JS code (1): [5]
Suspicious elements:
/AcroForm: [27]
/OpenAction: [1]
/JS: [4]
/JavaScript: [4]
getAnnots (CVE-2009-1492): [5]
Now we can see some statistics and information about the document. We can see some errors too, proof that it's not a normal PDF file:
Submitted by jesparza on Tue, 2011/07/26 - 00:19
As I mentioned in the previous post, just after Source Seattle some days ago, the ToorCon (also in Seattle) began. Some speakers took advantage of this to present the same or different presentations at both conferences. Friday the 13th was the opening day, with a small party, but the presentations didn’t begin until the following day. There were thirty talks in total, each delivered in a 15 minute period of time, with a short break for lunch. It was an entire day of presentations, from 8:30 till 10:30, quite a day!
Submitted by jesparza on Thu, 2011/06/30 - 10:10
Submitted by jesparza on Mon, 2011/06/27 - 22:58
Submitted by jesparza on Fri, 2011/05/13 - 15:09
After some time of inactivity in the blog I return with good news. I released the first version of peepdf last Friday. peepdf is a Python tool to explore PDF files in order to find out if the file can be harmful or not. The aim of this tool is provide all the necessary components that a security researcher could need in a PDF analysis without using three or four tools to make all the tasks. With peepdf it's possible to list all the objects in the document showing the suspicious elements, supports all the most used filters and encodings, it can parse different versions of a file, object streams and encrypted files. With the installation of Spidermonkey and Libemu it provides Javascript and shellcode analysis wrappers too. It is also able to create new PDF files and to modify existent ones. Thanks to the BackTrack team peepdf is included in the last version of this security distribution:
Submitted by jesparza on Thu, 2011/05/12 - 19:48
Recently our e-crime unit has detected a new banking trojan, named as Tatanga, with Man in the Browser (MitB) functions affecting banks in Spain, United Kingdom, Germany and Portugal. Like SpyEye, it can perform automatic transactions, retrieving the mules from a server and spoofing the real balance and banking operations of the users. Its detection rate is very low, and the few antivirus engines that can detect it yield a generic result.
The trojan in question is rather sophisticated. It is written in C++ and uses rootkit techniques to conceal its presence, though on occasion, its files are visible. The trojan downloads a number of encrypted modules (DLLs), which are decrypted in memory when injected to the browser or other processes to avoid detection by antivirus software. The modules are the following:
- ModEmailGrabber: It gathers e-mail addresses.
Coredb: It manages the trojan's configuration. The corresponding file is encrypted with the algorithm 3DES.
Comm Support Library: This module implements the encryption of the communication between the trojan and the control panel.
File Patcher: The function of this module is not clear yet. It is suspected that it is in charge of the propagation across folders containing multimedia, zipped or executable files.
Submitted by jesparza on Tue, 2011/03/08 - 18:00

|