Sex, Exploit Kits and Ransomware |
Each of us has his own preferences: some people love Lady Gaga or Justin Bieber, others Rocco Siffredi or Laura Lion. The love for the latter can be dangerous if you are not aware of security problems when you have a non-updated system, and it's possible you end with an infected system asking for money to recover the control of the machine.
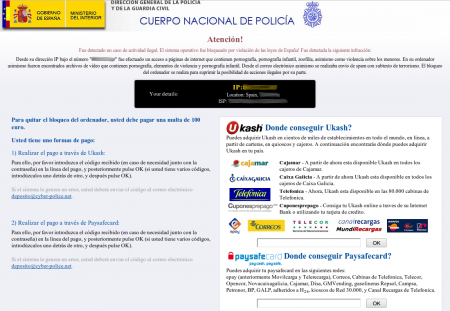
This was an interesting situation so I tried to help my friend. In this case, just after the desktop appeared, a full-screen window showed. It was a warning from the Spanish police ("Cuerpo Nacional de Policía") saying that the system had been blocked because it had been used to perpetrate illegal actions like child pornography, terrorism and violence against children: "Fue detectado un caso de actividad ilegal. El sistema operativo fue bloqueado por violación de las leyes de España!". A warning like this can be shocking for a normal user, so social engineering was working here. However, this warning was also asking for 100€ to be paid via Ukash or Paysafecard as a fine for this behaviour and in order to restore the system. This part can be a bit strange and maybe makes the victims call the police very quickly. Once this window appeared no other action was possible, like execute the Task Manager or return to the desktop, just enter a code to pay.
After analysing the system thanks to the Safe Mode, and knowing when it was used the last time, I was able to search for new files and clarify the actions performed before the infection. I was able to find the evil executable and, also, some interesting files like some *.idx files containing HTTP requests to a malicious domain, and a JAR file too. The URLs found were the following:
hxxp://car.foreclosuresinpa.info/content/v1.jarhxxp://car.foreclosuresinpa.info/w.php?f=23&e=0
These paths were familiar to me, reminding me of some kind of Exploit Kit, BlackHole, in fact. In this case the JAR file was including a CVE-2011-3544 exploit and the payload was downloading and executing the malware (DLL) served by the second URL.
The malware found (342e3d559d6ea9cbf4057769d4d76994) belongs to the Ransomware family, which block the system or encrypt the system files and ask for certain amount of money or ransom to recover the control of the machine. In this case, cyberdelinquents used social engineering techniques to try to cheat the users and obtain the money. The following are the most important actions performed by the malware:
- Creates a shortcut in \Documents and Settings\$USER\Menú Inicio\Programas\Inicio to execute rundll32.exe with the downloaded DLL, assuring its execution when the system is booting.
- Disable security of Internet Explorer security zones.
- Shows the police warning, an Internet Explorer window with the content of this URL in Moldova (online yet):
http://xxx.yyy.73.43/
- Also tries to download another DLL (3c47bae62499cb5a3cb98e4b753a5e69) from the following URL to steal FTP, VPN, IM, WebBrowsers and Poker applications credentials. It sends and receives data to/from 64.20.38.90:443, an IP located in the United States but in the range of an Ukrainian private customer.
http://xxx.yyy.73.43/images.rar
This sample was very easy to remove, just entering in Safe Mode and executing some kind of Anti-Malware or Anti-Spyware solution, or, manually, locating the shortcut in \Documents and Settings\$USER\Menú Inicio\Programas\Inicio and the related DLL and removing them. In this case, the filenames were 0.1998781520909214.exe.lnk and 0.1998781520909214.exe, but these names can be different in other cases. You can use a Live-CD to perform the same task and remove them.
It was also possible to bypass the malware block by launching another Internet Explorer window (Ctrl+N) and then clicking File/Open to execute explorer.exe and recover the control of the system.
This incident has occurred in many points of Spain (and other countries too) and some of the URLs are still alive. It's an ongoing campaign so be careful when watching certain sites ;)
yo fui victima de ese ataque
yo fui victima de ese ataque y en esa ruta no me aparecía nada y le pase un malware y tampoco encontró nada lo que hice fue restaurar el sistema :S:S:S
Re: yo fui victima de ese ataque
Buenas!
Como decía en el post, la ruta puede cambiar de una infección a otra. Una forma de localizar el binario era usando un software anti-spyware o anti-malware actualizados, aunque también podrías haber buscado qué archivos se crearon justo en el momento en que te apareció la primera vez la pantalla, y así localizar los ejecutables relacionados.
Un saludo!
Many variants
Past 15 days, i've seen 3 variants of it. And found 3 interesting things:
* it is multi-language: on a French Machine it displays a text in French with the French Gendarmerie Logo on it.
* on Windows 7, it uses a RunDLL command to launch, so it is not displayed by Autoruns with its by-default options.
* on XP, the latest version I've seen is replacing the explorer.exe on c:\windows and the malware is marked as coming from Belkin!!! Found no trace of explorer backup. I had to take a explorer.exe file from another XP machine to repair the infected one.
During the last 3 weeks, 5 people in my neighbourhood has been infected by those variants. It is not only spread through porn sites. Some of them got it on web sites illegaly streaming football matches.
Re: Many variants
Hi,
Yes, I have some screenshots affecting Spain, Portugal, Italy, France, Germany and England. I also have some information about it affecting more countries like Belgium or Netherlands. They have a PHP using geolocation, so depending on your IP it shows one page or another.
About the infection point, as you say, it can be any vulnerable site where bad guys have injected the Exploit Kit script. For example, during January and February a lot of Wordpress sites were compromised to lead to Exploit Kits, so maybe they have used this vulnerability or another to do it.
My first impression when I saw the behaviour of my sample was that explorer.exe was replaced, but later I realize that it was the same and that a simple execution of the real explorer.exe was a solution to take the control of the machine. It would be interesting taking a look at your sample...;)
Thanks a lot for the comments!!
Cheers!