Vulnerabilities
I've received a Christmas gift some hours ago. In fact there were two gifts but only one has survived the trip. They are from Russia...with love. Of course I'm talking about two e-mails I've received with two suspicious links. Even the e-mail bodies were suspicious, I think they have packed very quickly my gifts or they are not very attentive to me...:( The From field included "bankofamerica" and the Subject "Accountfrozen" so I suppose this means that my Bank of America account is frozen, right?
After some redirections we can find the typical obfuscated Javascript code made in BlackHole:
After decoding the Javascript code we obtain the next step, also related to BlackHole. This time I can only see a unique Flash exploit trying to download and execute a binary from the same domain where the exploit kit is located (shellcode is XORed with 0x28).
Submitted by jesparza on Thu, 2011/12/29 - 03:31
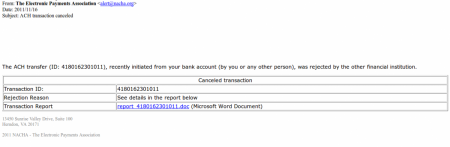
Our team (S21sec) has detected a ZeuS trojan distribution by email campaign that has been running for some days. The malicious emails include a link to a supposed report about a cancelled transaction, which is actually an HTML page that loads Javascript code into the victim’s browser. This code tries to exploit different vulnerabilities in Java, Flash and PDF to install ZeuS 2.0 on the system. This is one of the latest versions of ZeuS which uses P2P as part of its infrastructure (Murofet 2.0).
The subject of the emails detected so far is “ACH transaction canceled” and in the body of the mail there is information about a supposed transaction that has been cancelled. If the victim wants further information then they have to visit a link that contains a report about the transaction:
For a few seconds the victim sees a screen indicating that they must wait. Meanwhile 4 scripts, stored on different domains are loaded into user’s browser. They are little more than simple redirections towards the site where the code (that will attempt to perform the exploitation) resides.
Submitted by jesparza on Tue, 2011/11/29 - 14:02
According to a Kaspersky Lab article, SEO Sploit Pack is one of the Exploit Kits which appeared in the first months of the year, being PDF and Java vulnerabilities the most used in these type of kits. That's the reason why I've chosen to analyse a malicious PDF file downloaded from a SEO Sploit Pack. The PDF file kissasszod.pdf was downloaded from hxxp://marinada3.com/88/eatavayinquisitive.php and it had a low detection rate. So taking a look at the file with peepdf we can see this information: In a quick look we can see that there are Javascript code in object 8 and that the element /AcroForm is probably used to execute something when the document is opened. The next step is to explore these objects and find out what will be executed:
Submitted by jesparza on Mon, 2011/11/14 - 01:03
As I mentioned in the previous post, just after Source Seattle some days ago, the ToorCon (also in Seattle) began. Some speakers took advantage of this to present the same or different presentations at both conferences. Friday the 13th was the opening day, with a small party, but the presentations didn’t begin until the following day. There were thirty talks in total, each delivered in a 15 minute period of time, with a short break for lunch. It was an entire day of presentations, from 8:30 till 10:30, quite a day!
Submitted by jesparza on Thu, 2011/06/30 - 10:10
Submitted by jesparza on Mon, 2011/06/27 - 22:58
Submitted by jesparza on Fri, 2011/05/13 - 15:09
After some time of inactivity in the blog I return with good news. I released the first version of peepdf last Friday. peepdf is a Python tool to explore PDF files in order to find out if the file can be harmful or not. The aim of this tool is provide all the necessary components that a security researcher could need in a PDF analysis without using three or four tools to make all the tasks. With peepdf it's possible to list all the objects in the document showing the suspicious elements, supports all the most used filters and encodings, it can parse different versions of a file, object streams and encrypted files. With the installation of Spidermonkey and Libemu it provides Javascript and shellcode analysis wrappers too. It is also able to create new PDF files and to modify existent ones. Thanks to the BackTrack team peepdf is included in the last version of this security distribution:
Submitted by jesparza on Thu, 2011/05/12 - 19:48
After the Jailbreakme PDF vulnerability explanation I'm gonna publish the proof of concept of the same vulnerability for Foxit Reader. This is a patched vuln for this product so I suppose there will be no problem with that. Like I said, we can use a 116-bytes shellcode without the necessity of another exploiting stage, so I've modified this calc.exe shellcode for this PoC.
This exploit generates a PDF file which can be used against Foxit Reader in Windows XP and Windows Vista. This is functional only for the latest versions of Foxit Reader but it's very easy to modify it for other ones (there is an example in the exploit for the 3.0). You can find the python script in the Exploits section or directly here. Enjoy it!! ;)
Submitted by jesparza on Mon, 2010/08/23 - 23:18
| foxit40_type2.py |
Vulnerability: FreeType Compact Font Format (CFF) Stack Based Buffer Overflow [CVE-2010-1797] [BID-42241]
Affected product: Foxit Reader <= 4.0
Platform: Windows XP, Windows Vista
Type: Code execution
Publication date: 2010-08-23 |
Today has been released the source code of the Jailbreakme exploit, so maybe this explanation comes a bit late. In the update of the previous post about this subject I knew that I was right about the overflow in the arguments stack when parsing the charstrings in the Type 2 format, so here is a little more info.
After decoding the stream of the object 13 we can see the following bytes (talking about this file):
The selected bytes are the important ones for this exploit because the overflow occurs when parsing them. Like I mentioned, the Type 2 format is composed of operands, operators and numbers, and use the stack to push and pop values. This stack has a maximum size of 48 elements. We can understand better the meaning of these bytes with this tips:
Submitted by jesparza on Thu, 2010/08/12 - 18:49
Some days ago Comex published his JailbreakMe for the new iPhone 4 in the Defcon 18. The interesting thing is that in order to root the device he used a PDF exploit for Mobile Safari to execute arbitrary code and after this another kernel vuln to gain elevated privileges. I've being taking a look at the PDF files with peepdf and these are my thoughts about it.
The PDF file itself has no many objects and only one encoded stream:
The stream is encoded with a simple FlateDecode filter, without parameters, and if we decode its content we can see this strings, related to the JailbreakMe stuff:
As this object seems to contain the vulnerability we are looking for we'll take a closer look to this stream and what this is for:
Submitted by jesparza on Wed, 2010/08/04 - 00:40
ID: CVE-2007-0428 BID-22131 BID-22152
Product: WzdFTPD is a ftp server designed to be modular and portable, work under linux/win32/freebsd/openbsd, and to be entirely configurable online using SITE commands. It supports SSL, IPv6, multithreading, external scripts, and it uses Unix-like permissions and ACLs, with virtual users and groups.
WzdFTPD project also supports bandwidth limitation (per user, per group, or globally), group administrators, and per command authorization.
Scope: Remote Denial of Service
Severity: Medium
Timeline:
- [2006-12-26] Vulnerability discovered
- [2007-01-08] Vendor contacted (without answer)
- [2007-01-19] Vulnerability published
- [2007-01-31] Patched
Platforms: Any
Author: Jose Miguel Esparza
Affected versions: WzdFTPD < 8.1
Description: This vulnerability it's due to a bad truncation of blocks and later ruling out of the characters carriage return (\r), line feed (\n) and horizontal tab (\t) after authentication, resulting in a null character that the function chtlb_lookup is not able to handle.
ID: CVE-2007-04897 BID-25642
Product: PWLib is a moderately large C++ class library that originated many years ago as a method to produce applications that run on both Microsoft Windows and Unix X-Windows systems. It also was to have a Macintosh port as well, but this never eventuated. The library is used extensively by many companies for both commercial and Open Source products. The motivation in making PWLib available as Open Source was primarily to support the OpenH323 project, but it is definitely useful as a stand-alone library.
Scope: Remote Denial of Service
Severity: Low-Medium
Timeline:
- [2007-05-14] Vulnerability discovered
- [2007-07-09] Vendor contacted
- [2007-08-15] Ekiga patched
- [2007-09-11] Vulnerability published
- [2007-09-27] Pwlib patched
Platforms: Any
Author: Jose Miguel Esparza
Affected versions: Pwlib <= 1.10.0 (also the applications which use this library, for example Ekiga <= 2.0.7)
ID: CVE-2007-04924 BID-25955
Product: OPAL (Open Phone Abstraction Layer) is an implementation of various telephony and video communication protocols for use over packet based networks. It's based on code from the OpenH323 project and adds new features such as a stream based architecture, better support for re-use or removal of sub-components, and explicit support for additional protocols.
Scope: Remote Denial of Service
Severity: Low-Medium
Timeline:
- [2007-06-11] Vulnerability discovered
- [2007-07-09] Vendor contacted
- [2007-08-15] Patched
- [2007-09-17] New version released
- [2007-10-08] Vulnerability published
Platforms: Any
Author: Jose Miguel Esparza
Affected versions: OPAL <= 2.2.8 (also the applications which use this library, for example Ekiga <= 2.0.9)
Description: Thanks to an insufficient input validation of the Content-Length field of a SIP request it is possible to write a null byte causing a denial of service (crash) of the application using this library.
Details:

|