Yet another Oficla email campaign (CV) |
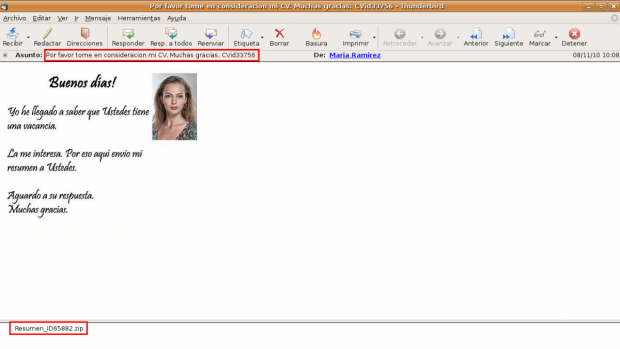
This time I've received a nicer e-mail, a woman sending me her CV!! with a picture of her included too!! :) In fact, she has included in the image some words too, a bit strange...
Again the same actors: Oficla and ZeuS. This time not Feodo downloading. Inside the zip file we can find the Oficla sample, with a medium detection rate. It connects with the domain showtimeru.ru (now it's down) to ask for URLs to download more malware:
http://showtimeru.ru/show/bb.php?v=200&id=428308300&b=0711_e&tm=6832
[info]runurl:http://1xx.1xx.1xx.46/test/esmilk.exe|taskid:8|delay:15|upd:0|backurls:[/info]The server response contained the same URL (active yet) as the DHL campaign, downloading the same version of ZeuS, different MD5.
Beware with women!! they are not trustful!! ;)