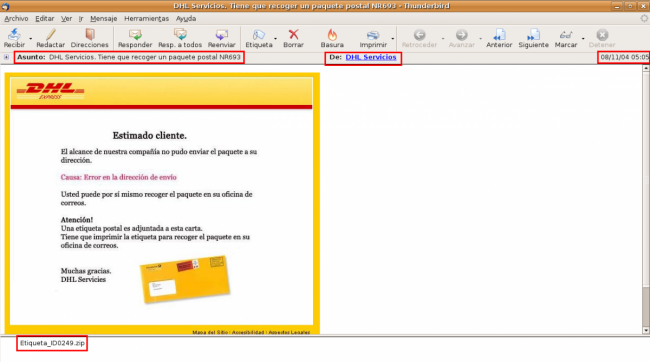
DHL e-mail campaign downloading ZeuS and Feodo |
This past month a new DHL campaign has been spreading malware in a zip file. The executable in the zip was identified (with a high detection rate) as Oficla by the Antivirus engines. This malicious code, with filename DHL_Etiqueta.exe, acts as a downloader asking a server the URLs it must use to download the other malicious files. It always uses in the requests the User-Agent Opera\9.64. These are the requests and responses in this case:
http://xxxxxx.ru/mydog/bb.php?v=200&id=428308299&b=2510_dhl&tm=1397
[info]runurl:http://1xx.1xx.1xx.xx/test/morph.exe|taskid:16|delay:15|upd:0|backurls:[/info]
http://xxxxxx.ru/mydog/bb.php?v=200&id=428308299&tid=16&b=2510_dhl&r=1&tm=1397
[info]kill:0|runurl:http://1xx.1xx.1xx.xx/test/esmilk.exe|taskid:17|delay:15|upd:0|backurls:[/info]
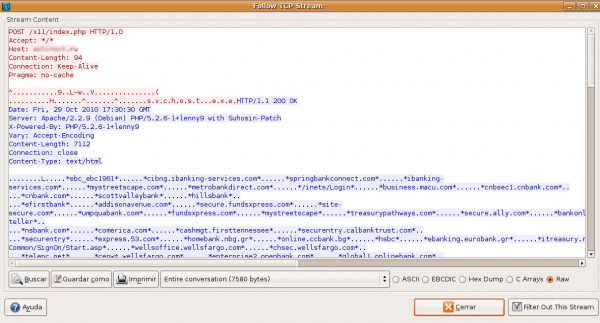
Both of the downloaded files, morph.exe and esmilk.exe, are banking trojans. The former is a sample of Feodo, with a low detection rate (7/41), which downloads the configuration file from a server after sending to it a POST request:
The latter is a ZeuS 2.0.7.0 with a medium detection rate (20/43). It connects with the domain mservicesonline.ru to download the configuration file and to send data to the C&C panel:
http://mservicesonline.ru/f0rum/gate.php
http://mservicesonline.ru/f0rum/ess.jpg
Like it's said in ThreatExpert the malware received by mail may spread itself by sending emails to some pseudo-aleatory addresses with different senders and bodies.